Install Root CA
- Build new stand-alone root CA, not attached to domain and give unique name.
- Log on to the server as the administrator and install Certificate Services to create a stand-alone root certification authority.
- Install Certificate Authority service only, IIS is not needed.
- Create a new private key
- Ensure the common name for the CA is unique.
- Change the validity period for the CA’s certificate to 20 years
Install Sub CA
- Build new enterprise subordinate CA and add to domain.
Add the following role services- Certification Authority
- Certification Authority Web Enrollment
- Online Responder
- Certificate Enrollment Policy Web Service (Might need to install this later)
- Setup type is Enterprise, Subordinate CA, create a new key, Cryptographic service provider (CSP): RSA#Microsoft software Key Storage Provider
Key length: 2048, Hash algorithm SHA1. Common name is the same netbios name as the original enterprise root CA if you are migrating from a stand alone CA, otherwise use a new name. Certificate Request: Save a certificate to file and manually send it later. Server Authentication Certificate: Choose and assign a certificate for SSL later. - Save the certificate request to file and manually send it later to a parent CA.
- Save this file to a shared location, it will be used later after other configurations need to be done.
- For the following few steps we will setup a CRL for the new offline Root CA and change the URL location of the certificate revocation list (CRL) distribution point to a location that is accessible to all users in you organization’s network while the Root CA is offline. It is necessary to do this because the offline root CA’s default CRL Distribution Points (CDPs) are not accessible to users on the network and, if they are left unchanged, certificate revocation checking will fail.
On the Root CA, Open Certification Authority - Right click on the RootCA server name -> Properties -> -> Extensions tab -> extension type: CRL Distribution Point (CDP):.
- Mark the line begins with “LDAP”, and click ‘Include in the CDP extension of issued certificates’.

- Mark the line begins with “HTTP”, and click remove.
- Mark the line begins with “file”, and click remove.
- Click on Add -> on the location, put: http://wwwca/CertEnroll/<CaName><CRLNameSuffix><DeltaCRLAllowed>.crl (where wwwca is the netbios name of the Sub CA server) Tick the following.

- Click on the line begins with “C:\Windows”, and make sure the only options checked are:

- Setup AIA information for the Offline Root CA, On the Extensions tab -> extension type: Authority Information Access (AIA):
- Mark the line begins with “LDAP”, and tick the following boxes

- Mark the line begins with “HTTP”, and click remove.
- Mark the line begins with “file”, and click remove.
- Click on Add -> on the location, put: http://wwwca/CertEnroll/<ServerDNSName>_<CaName><CertificateName>.crt (where wwwca is the netbios name of the Sub CA). Tick the following boxes.

- Click OK and allow the CA server to restart its service
- Mark the line begins with “LDAP”, and tick the following boxes
- From the “Certification Authority” left pane, right click on “Revoked certificates”-> Properties:
- CRL publication interval: 6 months
- Make sure “Publish Delta CRLs” is not checked
- Click OK
- Setup the root CA to issue certificates with an expiry date of 10 years (will issue to the Sub CA for 10 years)
- Change the following registry path on the Root CA -HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\CertSvc\Configuration\Root-CA\ValidityPeriodUnits
- Change the REG_DWORD decimal value to 10.
- This changes it to 10 years, so when the Sub CA gets a certificate, it won’t expire for another 10 years.
- Alternatively you can run from the command prompt – certutil -setreg CA\ValidityPeriodUnits 10 & certutil -setreg CA\ValidityPeriod "Years"
- Configure the offline root CA to support certificate revocation listing with Active Directory
- On the Root CA, Log on to the system as a Certification Authority Administrator.
- Open Command Prompt.
- Type the following, and then press ENTER. – certutil -setreg ca\DSConfigDN “CN=Configuration,DC=domain,DC=local”
- Type the following, and then press ENTER. – certutil -setreg ca\DSDomainDN “DC=domain,DC=local”
- Open Certification Authority.
- In the console tree, click the name of the certification authority (CA).
Where?- Certification Authority (Computer)/CA name
- On the Action menu, point to All Tasks, and click Stop Service to stop the service.
- On the Action menu, point to All Tasks, and click Start Service to start the service.
- From the “Certification Authority” left pane, right click on “Revoked certificates”-> All tasks -> Publish -> click OK
Manual steps to publish the Root CA CRL & AIA
- Copy the CRL & CRT file to the Sub CA
- On the Root CA, copy the files from C:\Windows\System32\CertSrv\CertEnroll to the same location on the Sub CA
- Publish the CRL & Root CA certificate to Active Directory
For this to work, you need to be a member of the Enterprise Admins group. Information is published to CN=Public Key Services,CN=Services,CN=Configuration,DC=C=domain,DC=local- From the Sub CA, the two files you copied before (.CRT and .CRL need to be used for this)
- Publish the Root certificate to AD - certutil -dspublish -f RootCACertificateFile.crt RootCA
- Publish the CRL information to Active Directory – certutil –dspublish -f CACRLFile.crl
- Add the Root CA to the AD trusted root area in Group Policy (Not really needed, up to you)
- On the DC, Start -> Administrative Tools -> Group Policy Management. From the left pane, expand the forest name -> expand Domains -> expand the relevant domain name -> right click on “Default domain policy” -> Edit. From the left pane, under “Computer Configuration” -> expand Policies -> expand “Windows Settings” -> expand “Security Settings” -> expand “Public Key Policies” -> right click on “Trusted Root Certification Authorities” -> Import -> click Next -> click Browse to locate the CRT file from the Root CA (C:\Windows\System32\CertSrv\CertEnroll) -> click Open -> click Next twice -> click Finish -> click OK.
- Issue the Sub CA a certificate from the Root CA server.
- Right click on the RootCA server name -> All Tasks -> Submit new request -> locate the subordinate CA request file (.req) -> Open.
- Expand the RootCA server name -> right click on “Pending Requests” -> locate the subordinate CA request ID according to the date -> right click on the request -> All Tasks -> Issue.
- From the left pane, click on “Issued Certificates” -> locate the subordinate CA request ID –> double click on the request –> Click the details TAB –> Copy to file –<subordinate_ca_server_name_signed_certificate>.p7b -> click Save.
- As an option only, on the SubCA, run the command bellow from command line to avoid offline CRL errors: Certutil.exe -setreg ca\CRLFlags +CRLF_REVCHECK_IGNORE_OFFLINE
- On the Sub CA, from command prompt, run – gpupdate/force
- Right click on the subordinate CA server name -> All Tasks -> “Install CA Certificate” -> locate the file <Subordinate_CA_Server_Name_Signed_Certificate>.p7b -> click Open.
- Right click on the subordinate CA server name -> All Tasks -> Start Service.
- Start -> Administrative Tools -> Group Policy Management.
- From the left pane, expand the forest name -> expand Domains -> expand the relevant domain name -> right click on “Default domain policy” -> Edit.
- From the left pane, under “Computer Configuration” -> expand Policies -> expand “Windows Settings” -> expand “Security Settings” -> expand “Public Key Policies” -> right click on “Intermediate Certification Authorities” -> Import -> click Next -> click Browse to locate the CRT file from the subordinate CA server (C:\Windows\System32\certsrv\CertEnroll) -> click Open -> click Next twice -> click Finish -> click OK.
- Logoff the domain controller.
- By default, IIS 7.0 request filtering blocks the plus sign (+), which is used in the URL of delta CRLs. To allow delta CRL retrieval, modify the IIS configuration by setting allowDoubleEscaping=true on the requestFiltering element in the system.web section of IIS configuration. For more information about IIS 7.0 request filter configuration, see IIS 7.0: Configure Request Filters in IIS 7.0.
appcmd set config /section:requestfiltering /allowdoubleescaping:true
Appcmd.exe can be found – %windir%\system32\inetsrv
Installing and configuring Online Responder (OCSP)
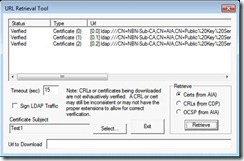
Testing CDP, AIA & OCSP information
- To Test CRL & AIA on client certificates, export any client certificate to a .CER file. Run the following command against the .CER file –
certutil -url file.cer or certutil -url file.crl
http://eyalestrin.blogspot.com/2010/07/windows-2008-r2-certification-authority.html
http://security-24-7.com/windows-2008-r2-certification-authority-installation-guide/

Dear Marc,
Just wanted to thank you from the bottom of my heart. You wrote the far best article about Microsoft CA. It’s amazing how everything is working now. THANKS!
marc, this is a great write-up. Can you clarify a little more about step 7 under Install Sub CA. Or is that an overview of steps 8-14? Or is there something we need to setup under step 7?
Hi Marc! Had to set a PKI up again the other day and this really helped – many thanks! Excellent article!
This article greatly appreciated!
Great, concise piece. My question is on step 5 of the “Install Sub CA” procedure, specifically “Common name is the same netbios name as the original enterprise root CA”. So if I install a new root CA, not joined to the domain, with a NetBIOS name of, say RootCA, that the CA name of my subordinate should be “RootCA” as well?
I beleive if you have a offline CA for the root with CN= RootCA and if you are building a subordinate CA to issue certs then you will use the CN of the subordinate CA (CN=Issuing CA). It’s consistant with Microsoft documentation- Please let me know if otherwise, i am currently documenting the process. Link to article. http://technet.microsoft.com/en-us/library/cc772393%28WS.10%29.aspx
I have updated the documentation about the naming of the Sub CA, step 5 under “Install Sub CA”. This doco was originally written for migrating from a stand-alone CA to a two tier solution.
Does the ROOT CA and the SUB CA replicate the certificates? The manual looks great furder btw. Just need to be sure.
[…] => Example Step by Step: https://marckean.wordpress.com/2010/07/28/build-an-offline-root-ca-with-a-subordinate-ca/ […]
[…] […]
Excellent Article … No errors , Looking like this article for long time.
This resource was invaluable! Just quickly, after following your guide I am seeing duplicated (x2) RootCA certificates in the trusted root store and likewise duplicated (x2) SubCA certificates in the Intermediate store. Is there any reason this is happening and is it by design?
You could probably ignore the duplicates, during the certificate exchange one (at random) will be used. So no harm having more than one. You could delete the duplicate is you like, as long as you’re sure it’s definitely a duplicate.
Marc
Great article really helped me understand how to setup a true offline root CA. The MS press books do not show you how to do it which is pretty sad. I do have a question though on setting up the CDP and AIA extensions. I saw you used the HTTP to specify where the CRL is located is thier other ways to set it up with HTTP? Also can I use HTTP without installing the webservice? I’ll most likely lab this to find out myself but I’d like to hear your thoughts on it. The most difficult subject in ADCS to me has been confiruing CDP/AIA extensions. Considering ADCS is a big part of the exam I would like to make sure I have a firm grasp on it.
I think HTTP is your only option. If you have a look at other large companies that use SSL certificates, they all use an HTTP CRL URL.
I have been trying to do this reading the white papers from Microsoft, what they left out you highlighted and this into a really nice step by step procedure to follow. Your instructions worked the first time for with no issues.
Thanks!
I have a question the following section “Install Sub CA” (step 1-12) & (2-4). For the following: http://wwwca/CertEnroll/%3CServerDNSName%3E_%3CCaName%3E%3CCertificateName%3E.crt do we use “wwwca” or do we use our own netbios name of the issuing CA?
Your own one is fine
Thank you Marc,I will try that- Do you also have good directions on creating auto enrollement for Domain Controller’s and SSL creating SSL templates? Thanks
Hi we are running a multiple domain forest. We currently have 2 domains in our forest. We have a dedicated Forest Root Domain called “X.local”. The other domain “Y.corp” is used for Users, Computers, etc… We want to setup a two tier PKI infrastructure (Stand Alone offline Root CA and subordinate Enterprise CA)
that will provide certs to users, computers etc.. on the “Y.corp” domain.
From what I found online the following command needs to be run against namespace of the forest root domain.
certutil -setreg ca\DSConfigDN “CN=Configuration,DC=X,DC=local”
As for the following can you tell me against which domain am I supposed to run this against? Is this also for the Forest root domain?
certutil -setreg ca\DSDomainDN “DC=domain,DC=local”
That’s a good question. You are running both (certutil -setreg ca\DSConfigDN “CN=Configuration,DC=X,DC=local”) and (certutil -setreg ca\DSDomainDN “DC=domain,DC=local”). My guess would be to run both against the domain where your users and computers are in the Y.corp domain. This is just a guess though, sorry I am not 100%. I think it all depends which domain the Subordinate CA is a member of.
Many thanks for that Marc. This helped me a lot.
Very clear and concise article, thankyou. Unfortunately, I had followed another article that advised to remove LDAP from the CDP and AIA on the offline RootCA. Are you able to confirm what the default values are so I can add LDAP back in?
I’ve followed the instructions. However, when I request a certificate using “mmc\certificates\personal” right click and select “Request a Certificate” the enrollment fails. The error says “The RPC server is unavailable”. During the enroll process I looked at the properties and everything looked ok. Any ideas? The domain controller previously had Cert Services installed. But I have since removed them.
[…] https://marckean.wordpress.com/2010/07/28/build-an-offline-root-ca-with-a-subordinate-ca/ […]
Very nice article. just up to the mark. this is wat i required.
hatts off to you….
Thanks for sharing such a nice article , very precise and to the point.
Thank you for the post really useful !!!
Very Good Article, Thanks Marc.
I am looking to migrate my standalone root CA to Two tier architecture, with offline standalone CA and Enterprise Sub CA. Can you please help me on this.
Thanks, Vikram
Hi Marc, I also looking for the same…whether we can use the same procedure mentioned above doing some tweaks
….Thanks
Snehal
[…] cut a long story short – I found an excellent resource online right here. Hopefully the author doesn’t mind the link, but this is a rundown on exactly how I […]
great document. But, i have a question on the command certutil -setreg ca\DSConfigDN “CN=Configuration,DC=domain,DC=local”. what domain i should use for the DC=domain? or should I just type “domain”? your reply is appreciated.
I also am trying to see if that is correct. I put “domain”, as stated, and then decided to stop to get clarification on that point. Also, is this line correct: “CN=Public Key Services,CN=Services,CN=Configuration,DC=C=domain,DC=local”, seems like there might be an extra C= in there. Thanks if you can help clear these points up.
Marc, I wanted to write itself about it, but your article is so successful that I simply decided to ask you to give me permission to publish its Russian translation on my blog.
Thanks
Go for it, thanks
Just a quick question, on step 12 of the sub root setup. “Click on Add -> on the location, put: http://wwwca/CertEnroll/.crl (where wwwca is the netbios name of the Sub CA server) Tick the following. ”
Is there reason you use the NetBios name instead of the FQDN?
What are the steps to add another subCA server at my second location? I already have offline root CA and subCA at the main office.
Nice job, everything worked from A to Z. For Online Responder and Revocation Configuration you can use this:
http://technet.microsoft.com/library/cc772393(v=ws.10).aspx
Thanks!
Hi there! Would you mind if I share your blog with my zynga group?
There’s a lot of people that I think would really appreciate your content. Please let me know. Cheers
Sure, no problems
thx for the article! one question regarding to the offline root ca. i have the same szenario but the point with the cdp/crl is a little but confusing for me.
so, whtat is best practise? to have a cdp in the root certificate or not? i have also a online sub ca and when i ´ll revoke the sub i need a crl in the root or not? thx and sry for my english :-)
Recently came across this article and it worked great. Good Article. If I want to add a second subordinate ca, do i follow the steps of the root ca (with regards to changing the CDP and AIA locations) for the second sub to see the same files and templates ?
Yes, but with two sub CAs, you need to publish the CRL to both sub CAs in case one is offline. Give each their own hostname resolvable internally and externally. You’ll need to publish the two HTTP CRL locations.
Great article.
Do you know what the possible pitfalls of following this approach when the domain already has an existing enteprise root?
Currently it has only issued web server certs and the standard certs to the DCs.
I’m fine with getting the root cert from the new offline root and publishing that to AD as above, and manually to the web servers. However the bit I’m struggling to recreate in a test lab is how the 2 enterprise CAs (one old Root and new Sub-Issuing) sit together in AD. I was hoping to see them both in Enteprise PKI, but I only see the original Root (however I do have an error on Enrollment Services Container as I didn’t do the CRL namespace remapping and it’s 2am now :-)
Gr8 man, it was helpful, my configuration is now complete without any issues….
Hello, its pleasant article regarding media print,
we all be familiar with media is a wonderful source
of facts.
[…] https://marckean.wordpress.com/2010/07/28/build-an-offline-root-ca-with-a-subordinate-ca/ […]
Everything works so far except for this step:
3.Publish the CRL information to Active Directory – certutil –dspublish -f CACRLFile.crl
I am using the name of the crl file. The error I get is:
ldap: 0xa: 0000202B: RefErr: DSID-031006E0, data 0 1 access points ref 1: ‘domain.local’
Certutil: -dspublish command failed: 0x8007202b (Win32: 8235)
Certutil: A referral was returned from the server.
I think the problem is the domain.local setting. Is it set that way because the root is not on the “real” domain? That part confused me a little.
Thanks.
FWIW – I just backed up a few steps and put in the domain string instead of domain.local and a new CRL was issued, I copied it over and ran the step above successfully.
Hey Marc
Brilliant and amazing, a perfect installation, what a pleasure. Am applying it on two separate sites and running the EnterpriseCA machine as a 2nd DNS non-global catalogue domain controller on each the same, and am now going to install Exchange 2007 x64 server with it as well, and deal with the full Online Responder installation later. Am hoping that I can now host an independent email server with acceptable security on the net incorporating own certificate, what do I know, ha ha. Great stuff and so useful, cheers. John
I do think this is a fantastic web-site and I’ll be coming back again to learn even more.