On June 22 Microsoft announced the new Azure Information Protection, which is basically an upgrade of the existing Azure Rights Management (Azure RMS) by adding the functionality of Secure Islands which Microsoft aquired late last year.
Companies and business historically have a logical perimeter, that perimeter contained the majority of business activity and IT services were accessed internally. This is in comparison to now where people access IT business services from anywhere. As employees become more and more mobile, IT admins start to punch stacks of holes in corporate firewalls. These days, all user activity is happening outside the perimeter of the company.
Sensitive data leaves companies every single day and normally ends up in the wrong hands. As most of the data is already in the cloud, it’s never been easier for people to share this data externally. Imagine if confidential data got leaked?
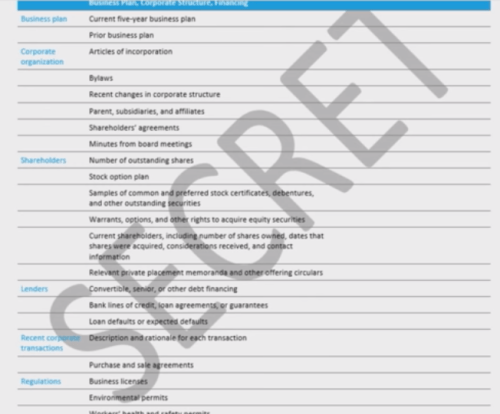
With Azure Information Protection, Microsoft is working at the document level, protecting the document in such a way that their products like Exchange and Office can deal with the documents and do what is necessary to stop leakage.
It’s all done in 5 simple protection steps:
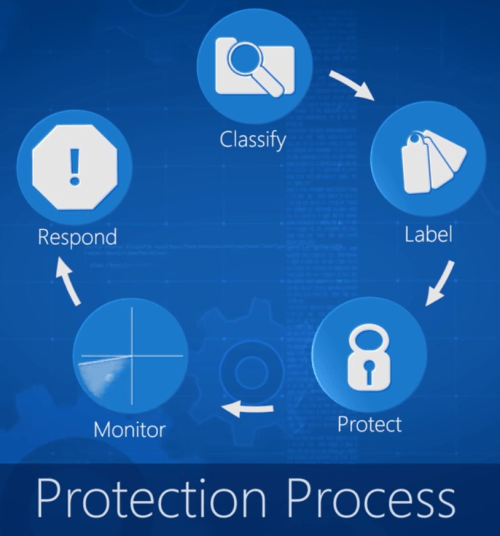
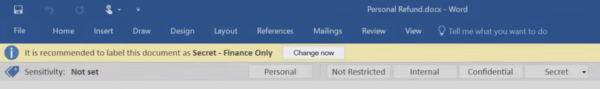
- Classify
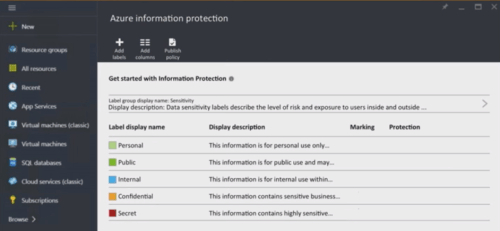
- To understand what is sensitive and what is not sensitive – Personal / Not Restricted / Internal / Confidential / Secret. Classification can be done manually, or with the case of DLP (Data Loss Prevention), this is done automatically.
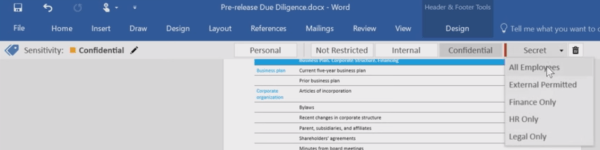
- To understand what is sensitive and what is not sensitive – Personal / Not Restricted / Internal / Confidential / Secret. Classification can be done manually, or with the case of DLP (Data Loss Prevention), this is done automatically.
- Labling
- Protect
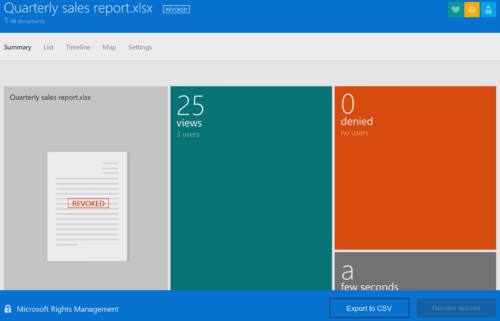
- Monitor
- Now that data has been classed and labeled, it makes it very easy to monitor it for possible abuse. You get emails for document activity as well as the ability to log onto the Azure RMS portal to see if the data is being abused and the locations in the world on a map as to where and what time the document was opened up. The picture of a bird indicates that the document is still floating around on the internet.
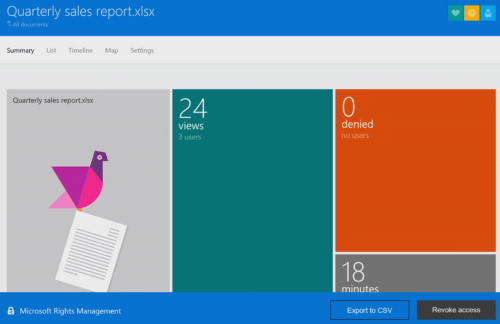
- Now that data has been classed and labeled, it makes it very easy to monitor it for possible abuse. You get emails for document activity as well as the ability to log onto the Azure RMS portal to see if the data is being abused and the locations in the world on a map as to where and what time the document was opened up. The picture of a bird indicates that the document is still floating around on the internet.
- Respond
This is all setup in the Azure portal where you can create custom policies.
More information: https://blogs.technet.microsoft.com/enterprisemobility/2016/06/22/announcing-azure-information-protection